Ransomware
November 20, 2023
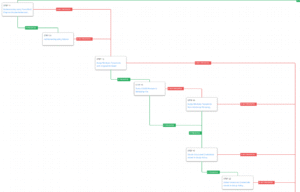
On November 15, 2023, CISA published an Advisory (AA23-319A) that disseminates known Indicators of Compromise (IOCs), Tactics, Techniques, and Procedures (TTPs), and detection methods associated with Rhysida ransomware identified through FBI investigations. In September 2023, AttackIQ released two new attack graphs in response to recent reports of activities involving Rhysida ransomware.
November 1, 2023
AttackIQ has released a new attack graph in response to the recently published CISA Advisory (AA23-284A) that disseminates known Indicators of Compromise (IOCs), Tactics, Techniques, and Procedures (TTPs), and detection methods associated with AvosLocker ransomware identified through FBI investigations as recent as May 2023. AvosLocker is known for conducting activities against organizations across multiple critical infrastructure sectors using legitimate software and open-source remote system administration tools.
October 9, 2023
AttackIQ has released three new attack graphs that aim to emulate the recent activities involving the commodity JavaScript-based downloader known as GootLoader.
September 20, 2023
AttackIQ has released two new attack graphs that seek to emulate the various activities carried out by the controversial Ransomware-as-a-Service (RaaS) known as Rhysida against multiple targets worldwide since its discovery in May 2023.
July 10, 2023
AttackIQ has released a new attack graph in response to the recently published CISA Advisory (AA23-187A) that seeks to emulate the activities carried out by the financially motivated and highly sophisticated criminal adversary known as TA505.
June 14, 2023
On June 14, 2023, the Cybersecurity and Infrastructure Security Agency (CISA) along with other US-based and international security organizations released a joint cybersecurity advisory (CSA) detailing the operations behind the LockBit ransomware attacks. AttackIQ has released a wide range of Attack Graphs emulating LockBit and other RaaS operators as part of CISA’s #StopRansomware campaign.
June 9, 2023
AttackIQ has released a new attack graph and two network security validation scenarios in response to the recently published CISA Advisory (AA23-158A) detailing the CL0P Ransomware Gang. This actor also known as TA505, is a financially motivated and highly sophisticated criminal adversary considered to be a major player in the e-crime scene that has left a significant impact on the global cybersecurity landscape.
March 3, 2023
AttackIQ has released a new fully featured attack graph that emulates the tactics, techniques, and procedures (TTPs) observed in cyberattacks involving Royal Ransomware.
September 8, 2022
AttackIQ has released a new attack graph emulating a Vice Society attack to help customers validate their security controls and their ability to defend against this threat actor and others who utilize similar behaviors.
August 11, 2022
AttackIQ’s Adversary Research Team has released a new assessment to test endpoint and network controls’ ability to prevent Zeppelin Ransomware.
June 15, 2022
AttackIQ has released a new full-featured attack graph emulating the tactics, techniques, and procedures (TTPs) used by the Conti Ransomware Group. Despite the group’s recent dissolution, Conti’s successful post-compromise tactics, techniques, and procedures will live on. This attack graph will help defenders test their cyberdefense technologies against the full range of techniques and procedures that Conti used – and which Conti’s former members, now in other ransomware groups, will likely continue to use.
June 2, 2022
AttackIQ has released a new scenario and assessment in response to US-CERT Alert AA22-152A, Karakurt Data Extortion Group