AttackIQ Ready
Turnkey Exposure Validation. Built and run by Experts.
Emulate real adversaries, validate control performance, and prioritize what truly puts you at risk—without the burden of managing it yourself.
Schedule a Demo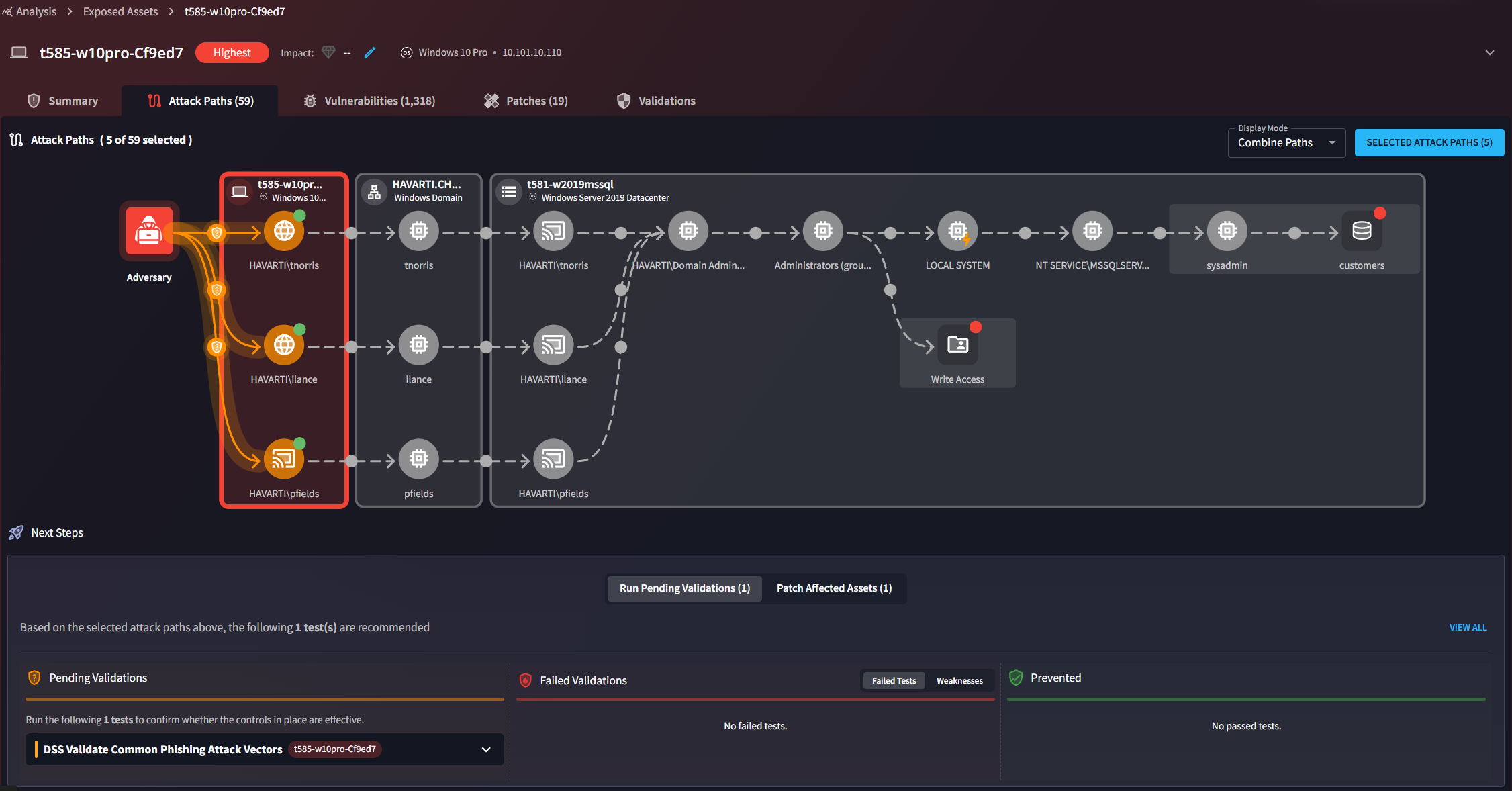
Adversarial Exposure Validation. Delivered as a Service.
No build. No maintenance. Just continuous, expert-led validation that strengthens your defenses.
Run Real-World Adversary TTPs
Execute emulations based on MITRE ATT&CK—no scripting, tuning, or setup required.
Expose Detection Blind Spots
Surface silent failures and security gaps across EDR, SIEM, firewalls, and perimeter controls.
Identify Exploitable Attack Paths
Map how adversaries can move through your environment to reach critical systems and data.
Prioritize High-Risk Exposures
Leverage hyperlocal threat intelligence and AI to focus on actively exploited exposures.
Remediate Validated Security Gaps
Apply targeted fixes with automated retesting to confirm control effectiveness.
Prove Security Improvements
Track control performance, remediation velocity, and risk reduction over time.
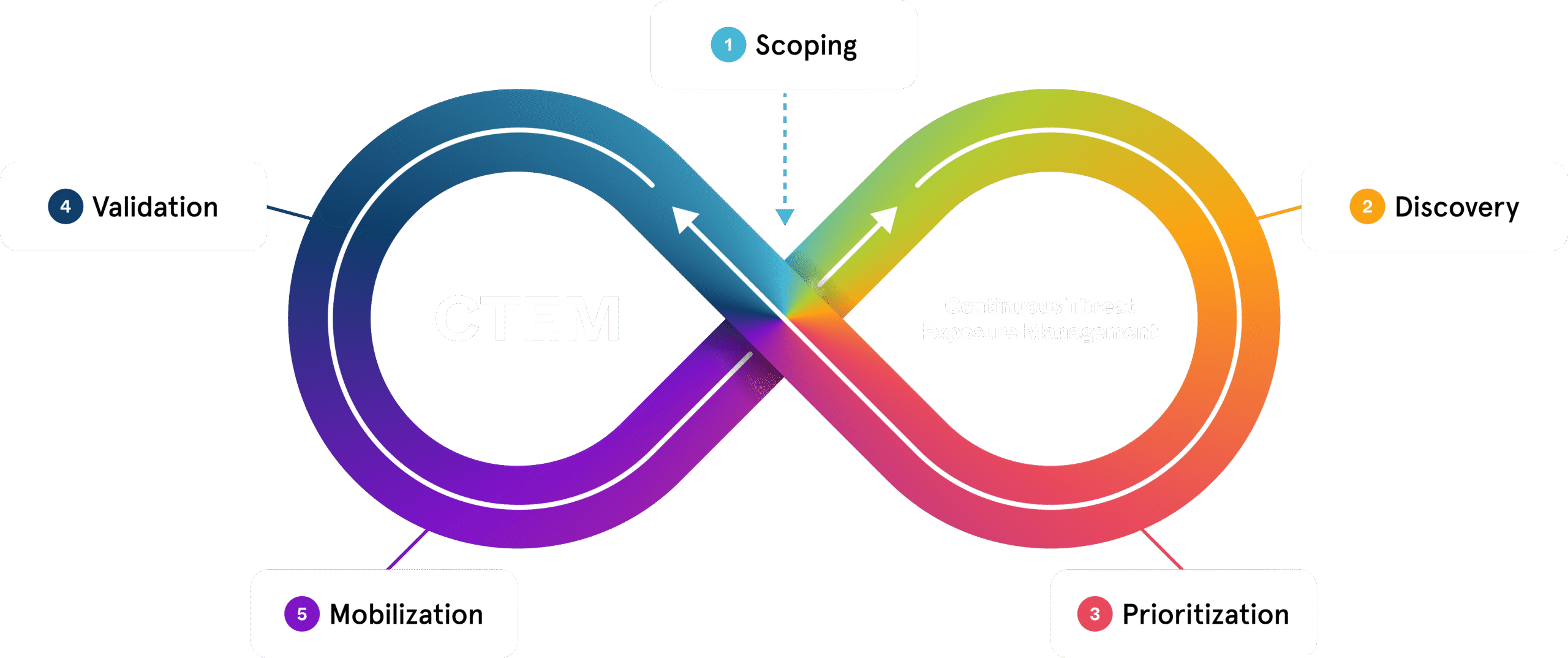
Engineered to Execute CTEM, End to End
Ready supports the execution of the CTEM framework from discovery to remediation. You define scope and objectives; we accelerate everything else.
Prove Control Effectiveness—from the SOC to the C-Suite
Showcase measurable risk reduction with expert-led testing, automated validation, and executive-ready reporting.
Track Security Performance Over Time
Monitor validation results, control gaps, and improvements across your environment.
Translate Risks for Executives and Boards
Deliver concise reports that map technical findings to business and mission impact.
Quantify ROI and Program Value
Measure outcomes like coverage, remediation speed, and reduced exposure.
Demonstrate Compliance Confidence
Generate audit-ready reports aligned to NIST, DORA, and cyber insurance standards.
Ready FAQs
Ready uses lightweight agents or test points that you deploy and control. We don’t require administrative access. You define what’s tested, when it runs, and where it happens—with full transparency and oversight.
Most customers begin validating exposures within two to three weeks. Once you deploy agents and configure scans, our experts handle test execution, analysis, and reporting. No lengthy setup or custom development is required.
No. AttackIQ experts handle all testing and analysis based on your priorities. Your team simply reviews the results and implements the recommended fixes.
Traditional BAS tools often require manual setup, scenario creation, and tuning. Ready delivers expert-managed adversary emulation, built-in attack path analysis, and prioritized remediation guidance. Instead of raw test data, you get actionable insights focused on real risk.
Ready uses safe, production-aware emulations that test defensive controls without causing outages or data issues. All tests are reviewed in advance to ensure they won’t disrupt operations.
You’ll receive immediate alerts along with vendor-specific remediation guidance. Fixes are prioritized based on business impact, and we help you retest to confirm the gaps are resolved.
Yes. Ready ingests data from platforms like Tenable, Rapid7, and Qualys, and integrates with Jira, ServiceNow, and other ticketing systems. API access is also available to support custom workflows.



