CTEM
CTEM, Operationalized
Continuously test your security controls, expose real risks, and protect what matters most.

What Is CTEM?
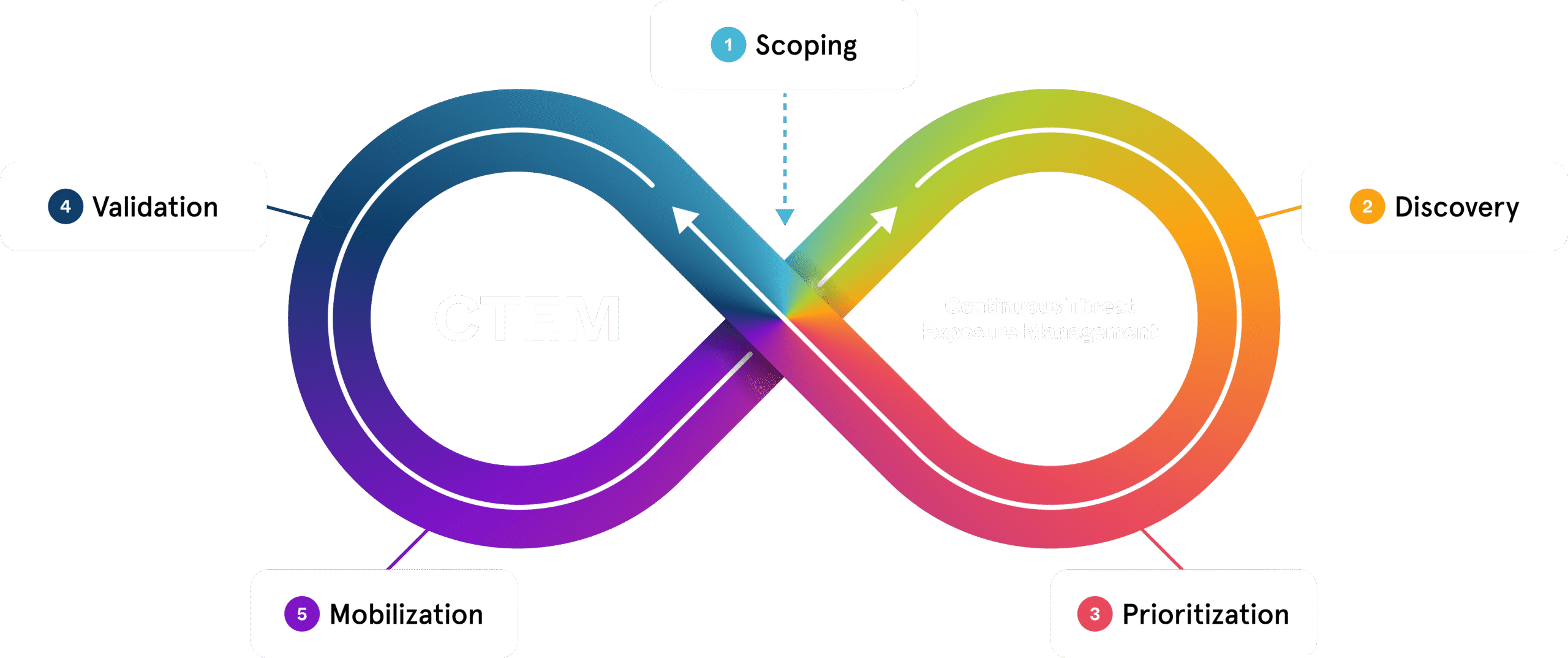
Continuous Threat Exposure Management (CTEM) is a proactive cybersecurity framework defined by Gartner. It helps organizations continuously identify, prioritize, validate, and remediate exposures across their entire attack surface—spanning assets, identities, and controls.
Unlike traditional approaches that rely on periodic assessments or static reports, CTEM creates an operational rhythm that aligns security efforts with business risk. It turns threat intelligence into action, integrates across teams and tools, and ensures your defenses are tested continuously—against the threats that matter most.
“By 2026, organizations that prioritize their security investments based on a continuous exposure management program will be three times less likely to suffer a breach.”
—Gartner, How to Manage Cybersecurity Threats, Not Episodes, August 21, 2023

“You’re not just testing controls—you’re proving readiness. That’s the leap CTEM enables. Security teams often don’t struggle with data, they struggle with decision-making. CTEM gives you the structure to prioritize based on what the business actually cares about: what’s exploitable and what’s impactful.”
Actualizing CTEM with Adversarial Exposure Validation
Get Actionable Guidance
The CTEM Lifecycle in Action
AttackIQ powers the CTEM lifecycle with adversary-informed validation at every stage, so your team can confirm what’s exploitable, prioritize real risk, and prove your defenses work.
Measurable Impact: The AttackIQ Advantage
Organizations using the AttackIQ AEV platform see clear gains in effectiveness, efficiency, and risk reduction.
Complete Adversarial Exposure Validation Suite
Flex
Agentless Exposure Validation
Ready
Managed Continuous Exposure Validation
Enterprise
Advanced Exposure Management at Scale
Command Center
Centralized Exposure Governance
Ideal for:
Enterprises or MSSPs managing exposure across multiple business units or clients
Learn MoreCTEM FAQs
While scoping is typically handled by your organization, AttackIQ stands apart in how it operationalizes the remaining phases of CTEM—especially in prioritization and validation. Our platform combines deep attack surface visibility with attack path analysis to identify the exposures that matter most. With the industry’s most comprehensive MITRE ATT&CK coverage, we emulate real adversary behavior in production environments, validate control effectiveness, and deliver clear, actionable guidance to reduce risk.
Yes. AttackIQ integrates with SIEM, SOAR, EDR, ticketing, and other tools to validate their effectiveness and enhance your existing workflows—maximizing the value of your current security investments.
Vulnerability management focuses on identifying technical weaknesses. CTEM takes it further—discovering, validating, and remediating exposures based on actual adversary behavior and business impact. It adapts to evolving threats, not just CVEs.
Yes. Pen testing and BAS are point-in-time exercises. CTEM delivers a continuous, structured approach to exposure management—ensuring insights from testing translate into operational improvements and risk reduction over time.
CTEM is the strategic framework. Adversarial Exposure Validation (AEV) makes it actionable. AEV automates threat emulation, validates control effectiveness, and provides evidence-based insight—bringing CTEM to life in real environments.
With AttackIQ, foundational CTEM capabilities can be deployed in 30–90 days, depending on environment complexity. Most organizations begin validating controls and identifying exposures within days.
Resource needs depend on your deployment model. AttackIQ Ready! offers a fully managed experience, while our Enterprise tier supports deep customization. In all cases, AttackIQ is designed to extend your team—not replace it.
CTEM adds a continuous validation layer across your tools and workflows. It improves detection, prioritizes remediation, and aligns security operations to real-world threats—boosting performance across your entire stack.
Effective CTEM requires continuous validation. AttackIQ automates this with scheduled testing based on threat profiles and environmental changes—ensuring defenses are tested as often as risk evolves.
Never Settle for Uncertainty
Validate Your Defenses
Take the guesswork out of threat exposure management. Validate your defenses with real-world attack scenarios and focus on what matters most—managing your risk.



