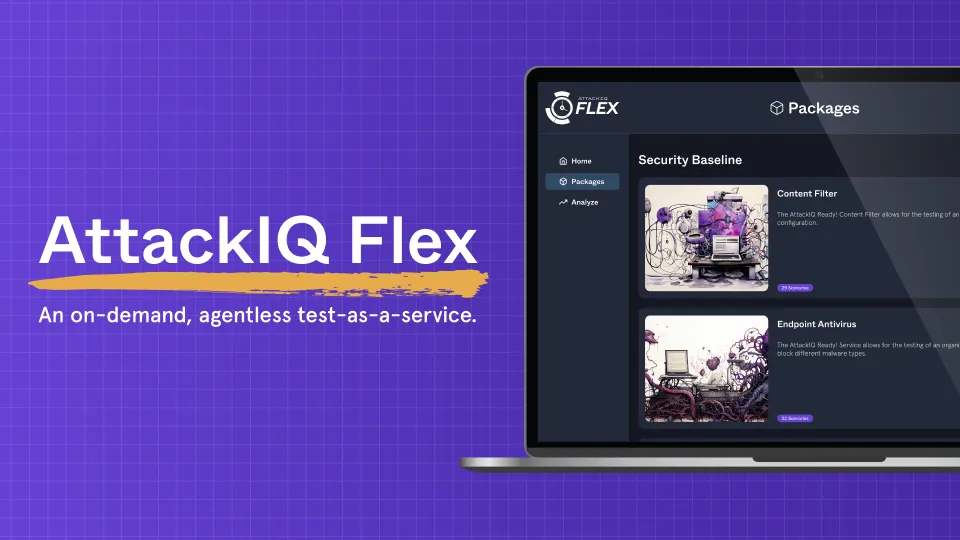
AttackIQ Flex
Agentless, On-Demand Exposure Validation.
Run production-safe adversary emulations in minutes. No agents, no installs, no commitment.
Try it FreeFinally, Exposure Validation That Works. On Your Terms.
Transform ad hoc testing into continuous validation that uncovers vulnerabilities other tools miss.
Self-contained test packages you can run on any device
Pay-as-you-go pricing with free credits to start
Prebuilt emulations aligned to real-world adversaries
Remediation guidance built in for faster fixes
Simple Exposure Validation—Anytime, Anywhere
Lightweight deployment gets you testing real-world attack scenarios immediately.
Choose Your Tests
Select from full adversary campaigns and security control baselines to validate your defenses.
Run Anywhere, Instantly
No agents. No installs. Execute production-safe tests on any device in your environment—Flex is fully self-contained.
Analyze and Remediate
View detailed results mapped to MITRE ATT&CK. Use built-in detection rules and mitigation guidance to close validated exposure gaps fast.
Adversary-Informed Testing Built for Speed
Validate your defenses against current threat intelligence without delays or lengthy procurement cycles.
Validate Exposure Using Real Attack Paths
Understand Your Risk in Minutes
Fix Validated Exposures
Verify Detection Coverage
Pay-as-You-Test Pricing That Scales With You
Start free, then scale based on actual usage. You maintain full control over testing frequency and scope—no overhead, no surprises.
FAQs
Flex is a lightweight implementation of the AttackIQ breach and attack simulation platform. Where Enterprise allows for more customization, Flex contains fully packaged scenarios. Click, run and done.
AttackIQ utilizes live malware samples that are saved and written to the local file system without execution. Using a hash comparison, Flex determines which samples were successfully planted on the endpoint. At the conclusion of the test, all staged files are promptly removed as part of the cleanup process.
To redeem credits, sign up for Flex and redeem within the product.
We’re always adding new tests and regularly provide curated content, including new adversary emulations as new attacker campaigns emerge.
There are two types of packages currently available. Adversary campaign tests and baseline tests. Baseline tests assess the efficacy of your core security controls while adversary emulations test your ability to withstand TTPs of known attacker campaigns.
No. Flex contains a smaller subset of content than enterprise.
Flex automatically generates a comprehensive report once the testing output is uploaded to the Flex portal. Specific report content varies depending on the report that is run.
The lightweight implementation of Flex means users can only run the packages available in the menu. Customers may wish to pick and choose multiple tests to run together.
Users can download a Flex test package and upload and execute on the endpoint of any supported OS.
Only Windows OS is currently supported with additional support coming soon.
There are innumerable uses cases for Flex. Below are some initial examples.
- Zero trust. Perform regular testing to validate the security of critical assets.
- SMB. Organizations with small network and security stacks, limited in house resources want to include security testing as part of security program
- Red team augmentation. Automate the scripting and execution of attack scenarios and penetration tests, allowing red teams to comprehensively test security controls, identify vulnerabilities, and provide mitigations
- Purple teaming augmentation. Design and execute attack scenarios against defenders with immediate feedback into people, process, and technology efficacy
- Regular self-managed security validation. Basic security validation and breach and attack simulation
- Fully managed security validation program. Conduct regular security validation but doesn’t have the staff to support in house testing
- Security posture assessment. Use Flex to validate security controls by scaling as many test points as you need for a representative sample of your environment.
- Managed service provider. Insurance provider or underwriter wants insuree to run a risk assessment on their network to determine coverage.
- Network consolidation, including M&A activity. Acquirer or parent organization wants to quickly bring on new branch networks into the corporate umbrella. Deploying agents takes too long for the request.
Additional Resources
Never Settle for Uncertainty
Validate Your Defenses
Take the guesswork out of threat exposure management. Validate your defenses with real-world attack scenarios and focus on what matters most—managing your risk.