AIQ Insights
Actionable. Incisive. Quantitative. Cutting-edge research into the art of adversary emulation.
Sign Up Today
A group of premier threat researchers and operators from around the world, AttackIQ’s Adversary Research Team (ART) develops cutting-edge insights on the latest threats coupled with actionable guidance on how to improve security readiness for customers and the public. Driven by intelligence and research, we help you validate your cyberdefenses against adversaries so you can proactively find and remediate gaps and achieve peak performance.
Stay up to date on our adversary research blog, adversary behavior studies, and demos. Sign up for AIQ Insights and we’ll deliver them straight to your inbox so you stay informed.
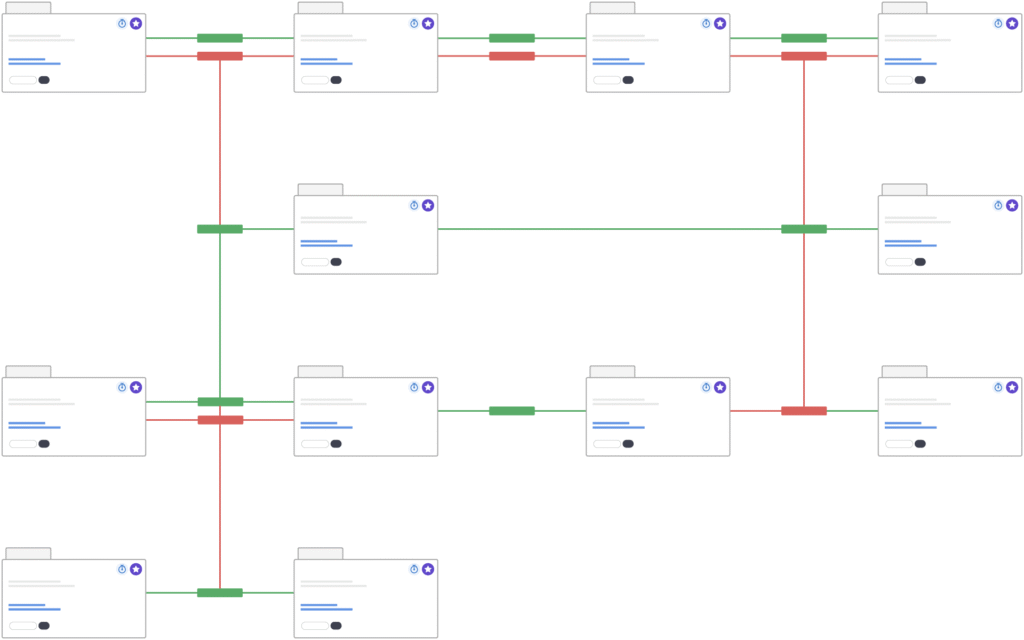
Adversary Research Team Workflow
MITRE ATT&CK-derived testing scenarios underpin much of the AttackIQ Security Optimization Platform. The AttackIQ Adversary Research Team builds scenarios and strings them into attack graphs to emulate adversary campaigns and test advanced cyberdefenses with realism and specificity, triggering AI and ML-based technologies and generating data about security program performance.
Step 1
Adversary behavior observed in the wild by AttackIQ, US-CERT, other open-source reporting across the threat intel community.
Step 2
Adversary Research Team responds to emerging adversary behavior and US-CERT alerts, analyzing tactics, techniques, and procedures.
Step 3
The Adversary Research Team develops scenarios and attack graphs to test defense capabilities, leveraging MITRE ATT&CK.
Step 4
Assessments and attack graphs released into the AttackIQ Security Optimization Platform and announced to customers and the public.
Step 5
AttackIQ advises customers on adversary behavior, assessment, attack graph usage, and how to leverage testing data.
Step 6
Adversary Research Team monitors threat landscape and studies defensive technology evolution continuously to stay ahead.
Data Study Report
Ending the Era of Security Control Failure
After months of analysis, AttackIQ is publishing a data analytic study of historic security control failures against top MITRE ATT&CK techniques – and what to do to improve security program performance.
Download Now
Actionable Insights
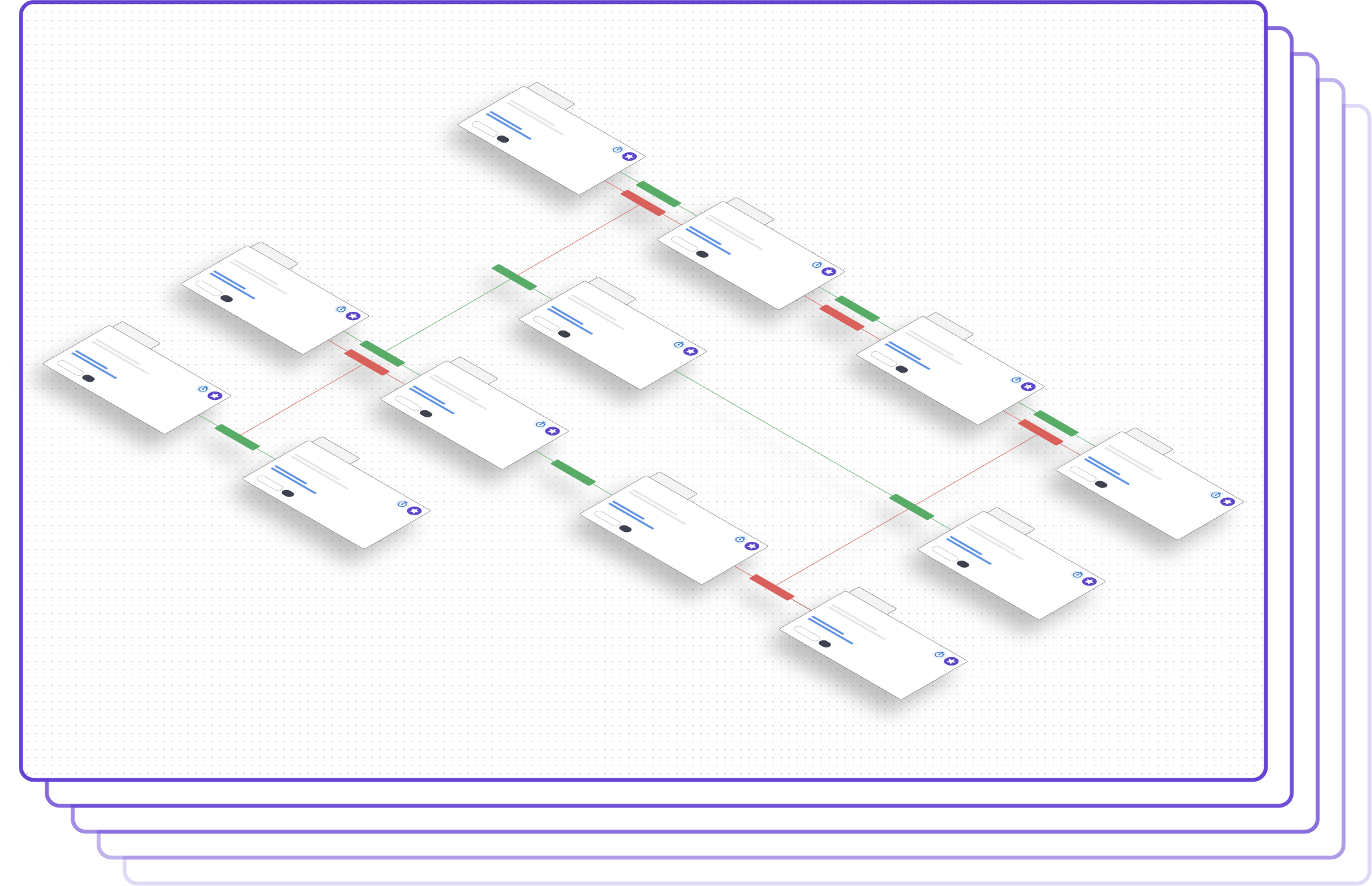
AttackIQ Assessments and Attack Graphs
AttackIQ produces emulation plans in the form of atomic scenarios and end-to-end attack graphs that emulate the adversary. The AttackIQ Security Optimization Platform runs scenarios aligned to MITRE ATT&CK in production, at scale, and can run multiple assessments concurrently against your security program. AttackIQ’s attack graphs string together techniques and procedures in a chain, emulating the adversary and testing machine learning (ML) and artificial intelligence (AI)-enabled cyberdefense technologies. Attack graphs make it easier for organizations to visually measure their defense performance against the adversary.
Subscribe to our ResearchLatest Research
US-CERT Rapid Response Assessments and Attack Graphs
AttackIQ responds within 24 hours to a U.S. government Computer Emergency Response Team (US-CERT) alert with an initial assessment and a blog for our customers to test their security posture against emergent threats. Within 72 hours, AttackIQ produces a comprehensive attack graph and blog to emulate the attacker, aligned to all of the MITRE ATT&CK tactics, techniques, and procedures in the alert.
Subscribe to our Research

Intelligence-Driven Insights
The AttackIQ adversary research team integrates open-source intelligence from MITRE ATT&CK and other analytic streams into the Security Optimization Platform to deliver a realistic threat-informed defense. In addition, the team drives research within the Center for Threat-Informed Defense, where AttackIQ is a founding research partner, to develop new operational concepts for effectiveness. Finally, the team communicates research findings to the public through the media and by presenting at events like BlackHat, SXSW, ATT&CKcon, and RSA, among others.
Check out our presentations at ATT&CKcon and SXSW and RiskyBiz.
Quantitative
Performance Data
The purpose of adversary emulation and the AttackIQ Security Optimization Platform is to generate quantitative insights that CISOs and security teams can use to improve their overall security program performance. Teams need to be able to answer questions from senior leaders, the board, and Congress: are we ready for the next attack? How prepared are we, really? By running AttackIQ’s assessments and attack graphs against your security program, you generate real-time performance data to make adjustments, identify investment areas, and improve team cohesion to counter attacks.
Subscribe to our Research
Measure Point-in-Time
Security Performance
Use adversary emulations to measure your security control performance at a single point in time.
Analyze Longitudinal
Performance Data
Run emulations against your security program automatically and continuously over time to measure performance.
Generate Performance Metrics Against Multiple Threats
Analyze your security controls’ performance against specific threats, running assessments and attack graphs concurrently against all of your security controls and test points.
Automate Tasks with Jupyter Notebooks
Teams can use AttackIQ’s open API through the dozens of Jupyter Notebooks embedded within the AttackIQ Security Optimization Platform to automate emulation-related tasks and generate insightful charts and graphs to help your management and operations teams make decisions and move forward more effectively and efficiently. You can use AttackIQ’s provided Jupyter notebooks to analyze threat coverage against security controls, analyze your entire security program against comprehensive adversary campaigns, to conduct product comparisons during a side-by-side comparison of security vendors, or other purposes. With AttackIQ’s open API, you can assign developers to generate new capabilities within the platform to meet your analytic needs. To learn more about using Jupyter notebooks.
Learn MoreAttackIQ Attack Graph Demos
Emulating the Conti Ransomware Family
Join experts from the AttackIQ adversary research team in this demo to see how to improve your security program performance by running ransomware emulations, beginning with the infamous Conti ransomware family.
Malware-Emulation Attack Graphs: SOGU and BlackCat
Join experts from the AttackIQ adversary research team in this demo to see how to improve your security program performance by running ransomware emulations, beginning with the infamous Conti ransomware family.
Purple Teaming with MITRE ATT&CK in the Oil and Gas Sector
Join experts from the AttackIQ adversary research team in this demo to see how to improve your security program performance by running ransomware emulations, beginning with the infamous Conti ransomware family.
The Adversary Research Team

Andrew Costis
Chapter Lead, Adversary Research
United Kingdom

Giovanni López
Principal Security Engineer
Spain

Francis Guibernau
Adversary Research Engineer
Argentina

Ayelen Torello
Adversary Research Engineer
Argentina