AttackIQ Blog
August 10, 2022
AttackIQ’s Adversary Research Team has released two new assessments to test endpoint and network controls’ ability to prevent widely utilized malware families.
August 4, 2022
The Center for Threat-Informed Defense recently published a methodology and calculator so that you can identify the top MITRE ATT&CK techniques that impact your sector.
August 2, 2022
AttackIQ’s Adversary Research Team has released a new Malware Emulation Attack Graph that emulates the Linux behaviors of the multi-platform backdoor known as SysJoker.
July 29, 2022
In this guest blog post, Bradley Schaufenbuel of Paychex writes about how security teams can leverage the MITRE ATT&CK framework to mount a “threat-informed” defense. This post originally appeared as an article in SC Magazine.
July 29, 2022
Hot off the press, IDC has released an IDC Business value White Paper, sponsored by AttackIQ, that explores the business value and benefits of using the AttackIQ Security Optimization Platform.
July 27, 2022
Organizations today find themselves at a critical turning point in the evolution of their vulnerability management efforts. New vulnerabilities are being published more quickly than teams can credibly analyze and remediate them (currently greater than 75 per day), while at the same time a serious talent shortage has developed. According to CyberSeek, the U.S. cybersecurity workforce has over 950,000 workers, with approximately 465,000 open positions.
July 13, 2022
With increasing online threats and a massive shift to remote work over the past two years, it’s no surprise that cybersecurity risks are a top concern for businesses in 2022. Cyber incidents top the Allianz Risk Barometer for the “most important global business risk” in 2022, accounting for 44% of the survey’s responses.
July 11, 2022
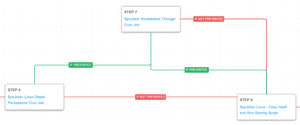
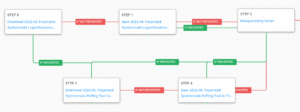
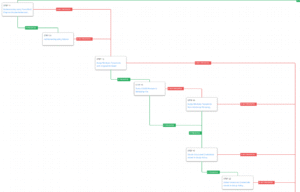
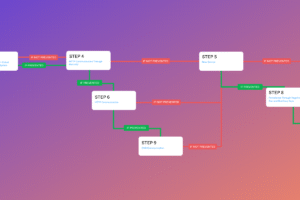
AttackIQ has released two new attack graphs that emulate different aspects of OilRig’s operations against multiple sectors around the globe. With these attack graphs, you can test and validate your defenses to improve cybersecurity readiness.
June 28, 2022
AttackIQ has released two new fully featured attack graphs emulating the tactics, techniques, and procedures (TTPs) used by likely nation-state adversaries that continue exploiting the Log4Shell vulnerability in VMware Horizon Systems.
June 24, 2022
In response to US-CERT Alert AA22-174A, AttackIQ has released new malware transfer scenarios to the platform and recommends validating security controls using previously released scenarios addressing Log4Shell and the VMware CVE-2022-22954 vulnerability.
June 15, 2022
AttackIQ has released a new full-featured attack graph emulating the tactics, techniques, and procedures (TTPs) used by the Conti Ransomware Group. Despite the group’s recent dissolution, Conti’s successful post-compromise tactics, techniques, and procedures will live on. This attack graph will help defenders test their cyberdefense technologies against the full range of techniques and procedures that Conti used – and which Conti’s former members, now in other ransomware groups, will likely continue to use.
June 3, 2022
AttackIQ has released a new fully featured attack graph emulating the tactics, techniques, and procedures used by the Karakurt Data Extortion Group recently reported in US-CERT Alert AA22-152.