Automate DORA Compliance
Meet Digital Operational Resilience Act (DORA) requirements with AttackIQ’s automated security testing, powered by the MITRE ATT&CK framework.
What is DORA Compliance?
The Digital Operational Resilience Act (DORA) mandates stringent cybersecurity measures for EU financial institutions and ICT providers, requiring full DORA compliance by January 17, 2025. By enforcing standards for risk management, incident reporting, and regular security testing, DORA strengthens digital resilience, helping organizations maintain operational continuity against cyber threats. This framework not only impacts financial entities but also extends to third-party providers critical to the financial sector.
Threat-Led Approach
The regulation emphasizes threat-led penetration testing, meaning testers consider real-world attacker behaviors to design their tests.
Mandated Testing
DORA mandates annual penetration testing for critical applications and systems, with advanced threat-led testing required every three years.
Critical Focus
Penetration testing needs to cover at least the critical functions and services of a financial entity.
Live Production Systems
DORA specifies that threat-led penetration testing should be performed on live production systems supporting critical functions.
How AttackIQ Helps You Meet DORA Requirements
AttackIQ’s breach and attack simulation (BAS) solution aligns with DORA’s Threat-Led Penetration Testing standards, enabling continuous testing to strengthen cybersecurity defenses and meet resilience and compliance requirements.
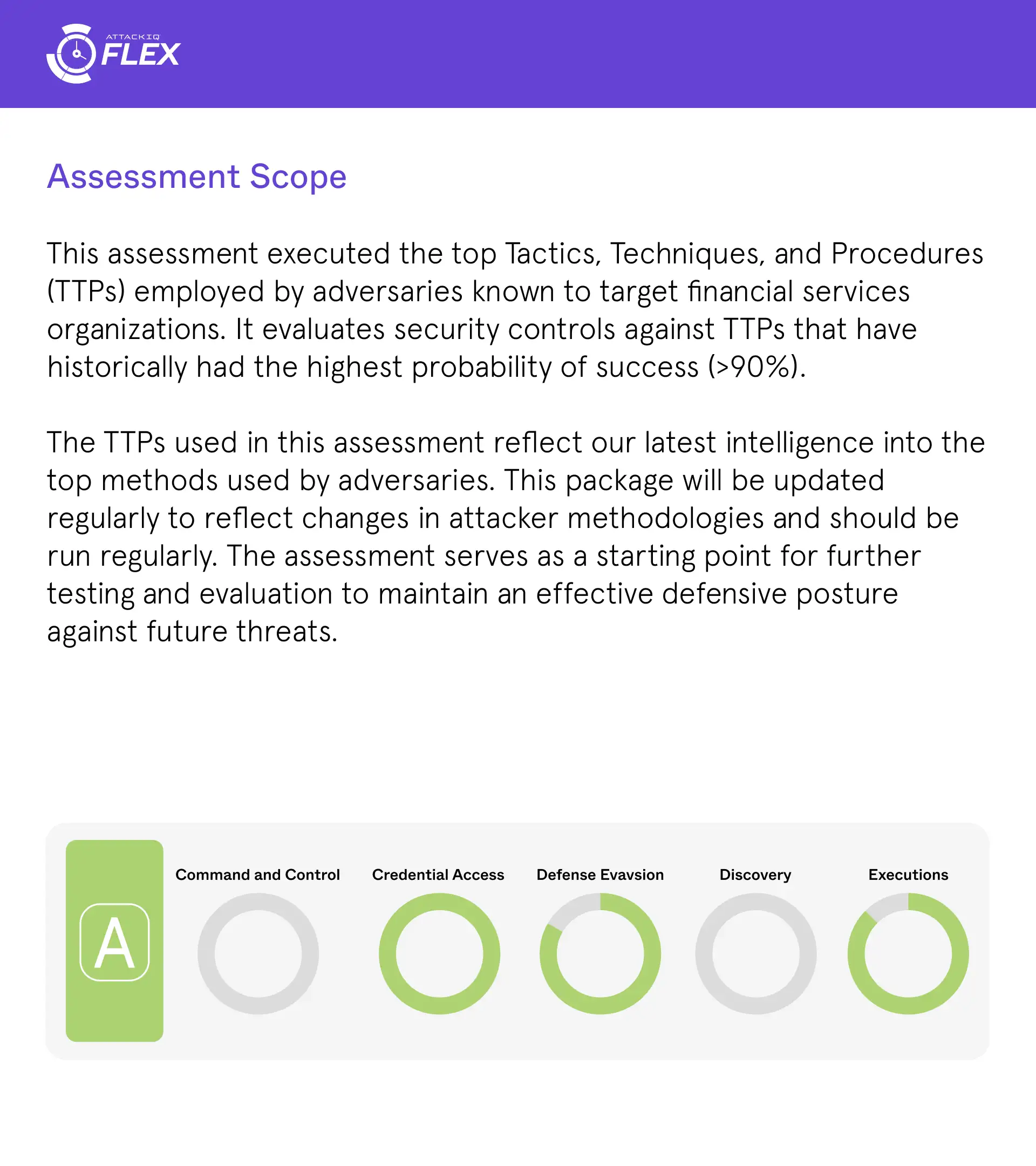
Tests Financial Sector Cyberdefenses
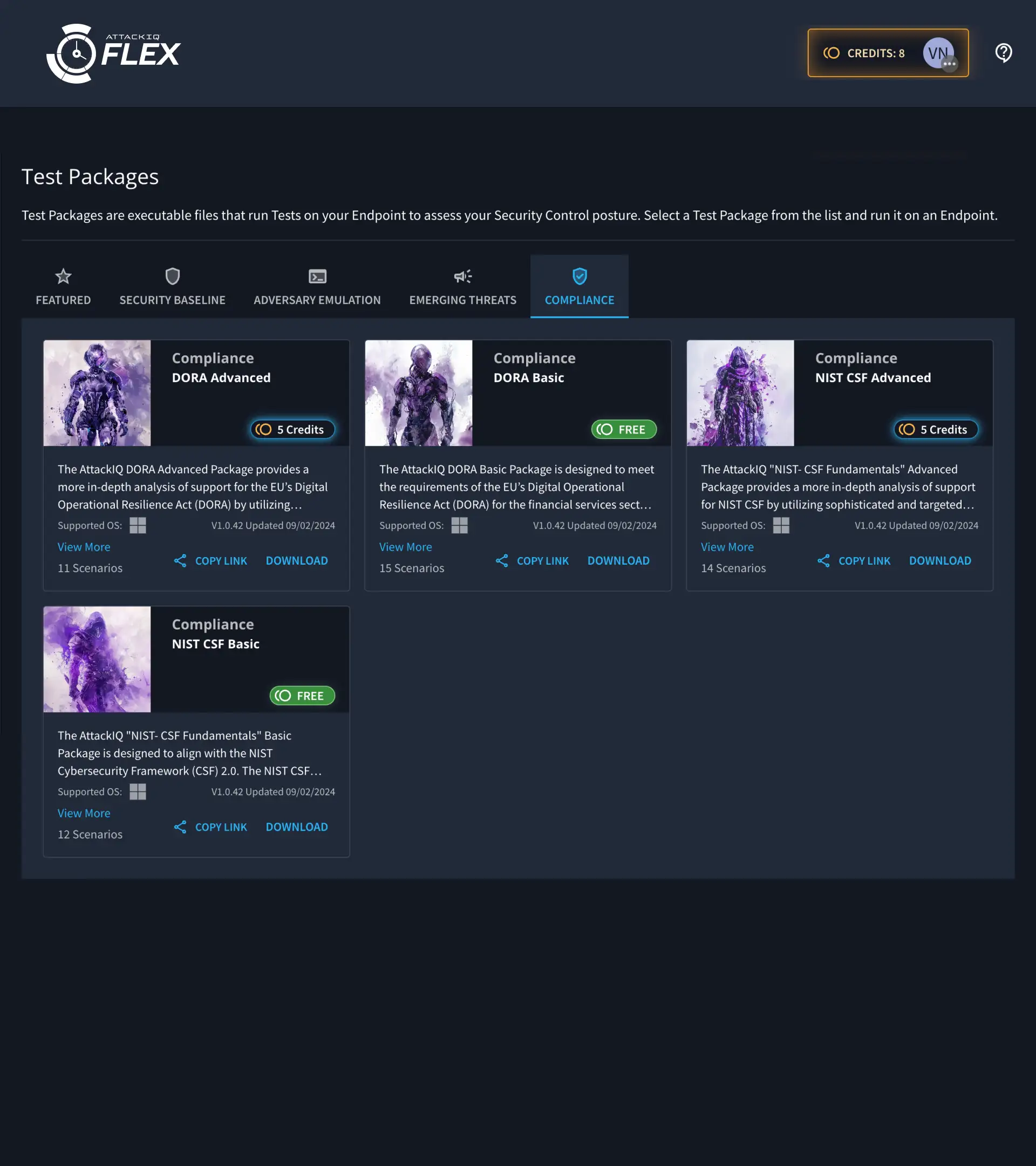
The DORA Basic and Advanced assessments test the most common adversary TTPs targeting financial services, based on the latest intelligence and threat research on top EU sector adversaries.
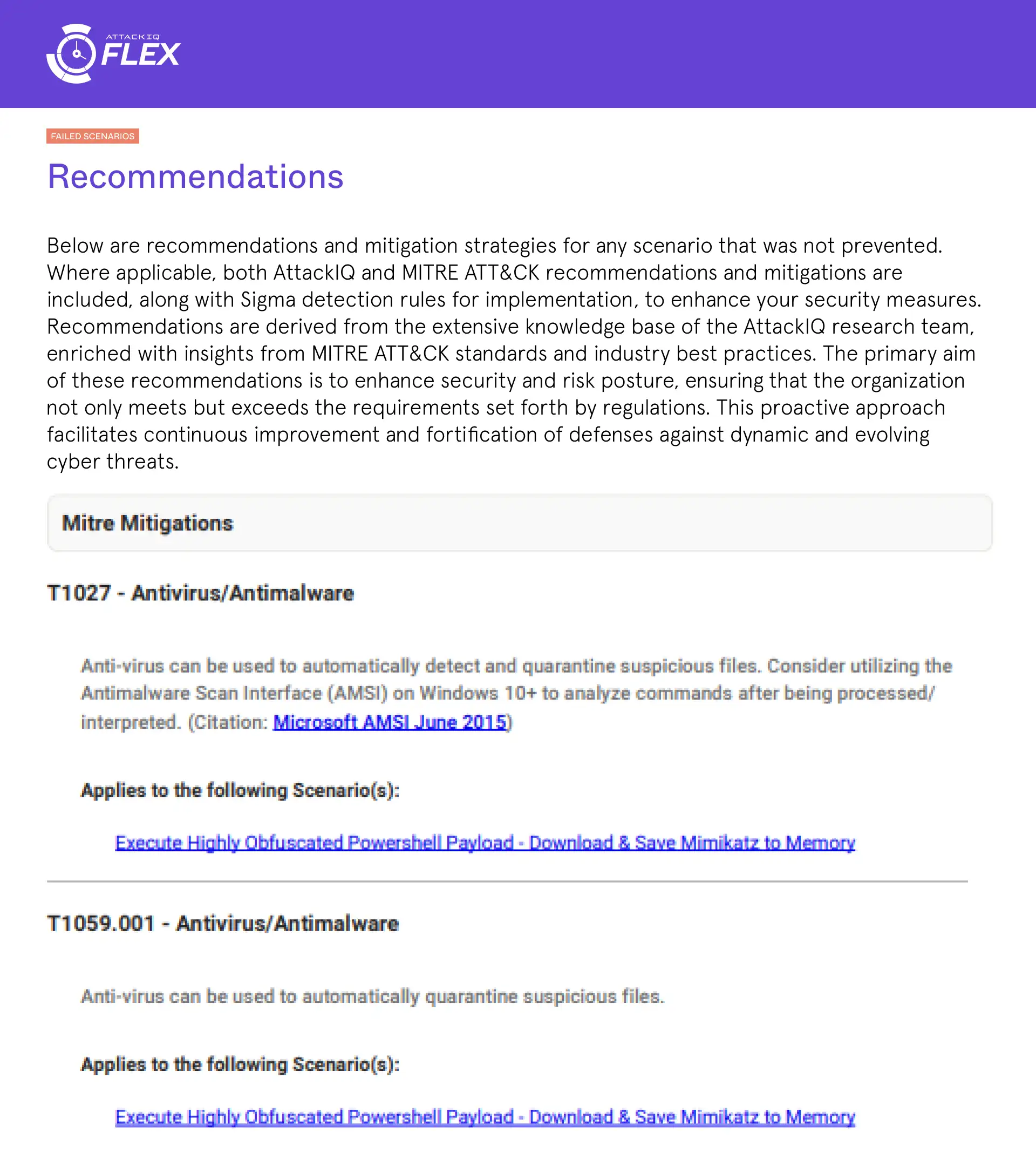
Recommendations and Mitigations
The DORA Assessment Report offers tailored recommendations and mitigation strategies for unprevented scenarios, drawing on AttackIQ’s expertise and insights from MITRE ATT&CK and industry best practices.
MITRE ATT&CK Aligned
The DORA assessment aligns with MITRE ATT&CK, providing actionable insights within a framework widely adopted by cybersecurity professionals across the globe. It ensures a structured approach to threat detection and mitigation efforts.
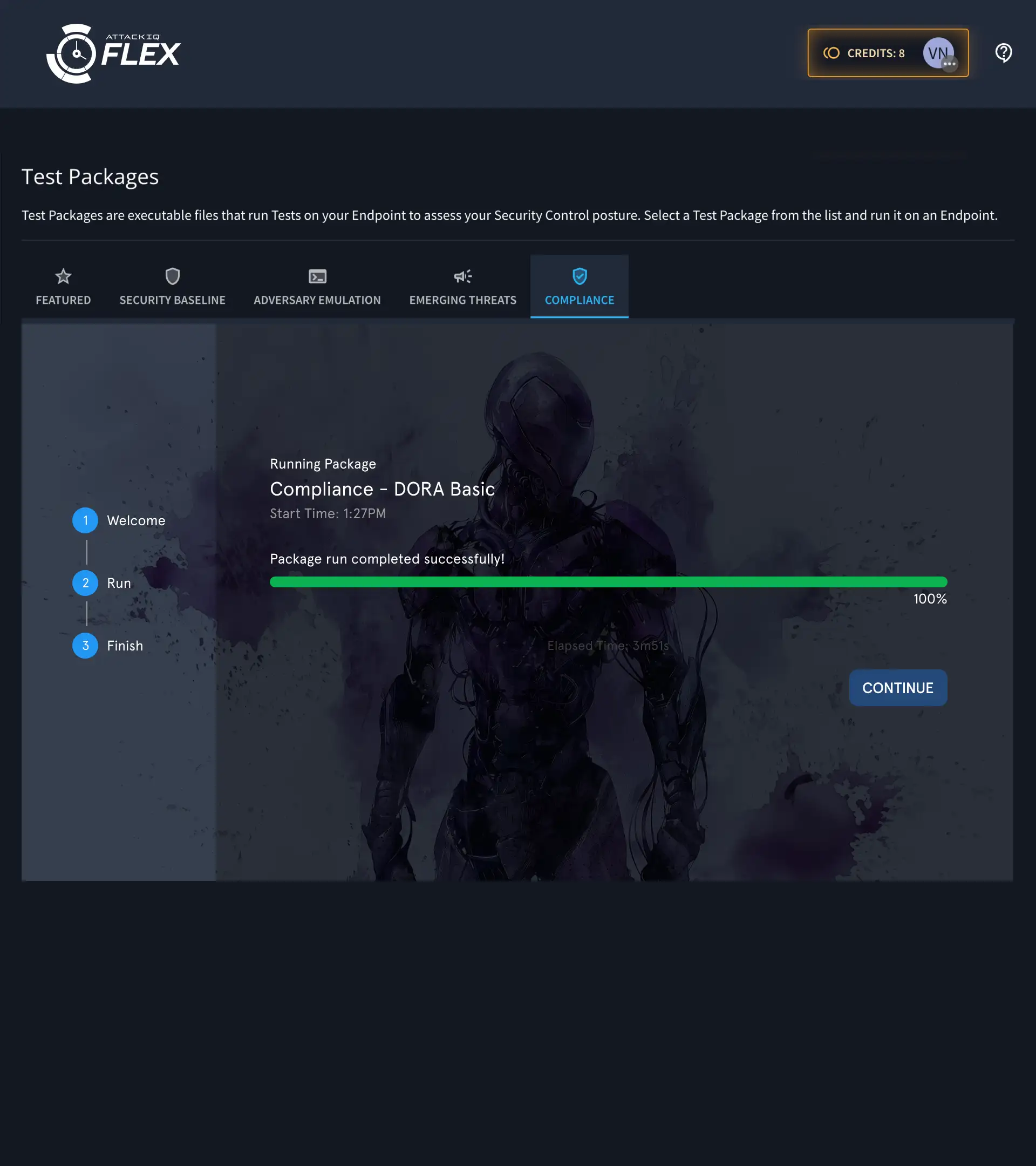
How AttackIQ DORA Assessments Work
AttackIQ’s DORA assessments leverage real-world adversary emulation to help you identify vulnerabilities, enhance detection, and improve your response capabilities.
Select Your Test
The Business Value of DORA Assessments
DORA assessments enable you to stay compliant, reduce cyber risks, and ensure ongoing operational resilience.
Assess EU Financial Sector Threat Actors
Leverage AttackIQ’s advanced adversary emulation software which fully emulates cyberattacks and the TTPs employed by real-world adversaries targeting the EU financial sector.
Testing for All EU Financial Institutions
Financial organizations of all types can harden their defenses and align with DORA, ensuring they can interdict threat actors before they can achieve their objectives.
Save Time and Resources
Provide an economical means of validating DORA security controls while balancing the need for expensive and time-consuming manual testing.
Live Production Systems
DORA establishes a clear oversight framework to ensure compliance. Failure to comply with DORA can result in various administrative, financial, and criminal penalties.
DORA Compliance FAQs
In summary, while DORA primarily targets the financial sector, it also extends to third-party providers that offer critical ICT services to financial entities, thereby affecting a wider range of organizations beyond traditional financial institutions.
The Digital Operational Resilience Act (DORA) legislation within the European Union (EU) is designed to ensure that financial institutions are well-equipped to withstand and recover from cyber threats and operational disruptions. DORA achieves this by setting requirements which include establishing and maintaining an information and communication technology (ICT) risk management framework, reporting and classifying ICT incidents according to a specific taxonomy, conducting regular testing of ICT systems and tools, and managing risks associated with third-party ICT service providers. DORA establishes a clear oversight framework to ensure compliance. Failure to do so can result in various administrative, financial, and criminal penalties.Threat-Led Penetration Testing (TLPT), MITRE ATT&CK, TIBER-EU, and Breach and Attack Simulation (BAS) platforms are core components that work together to support DORA. DORA has established the requirement for financial institutions to conduct regular TLPT. MITRE ATT&CK provides the blueprint and establishes the comprehensive library of attacker tactics, techniques, and procedures (TTPs) which can be used by TLPT. TIBER-EU, a European framework for simulating cyberattacks, helps define best practices for conducting threat informed red teaming exercises.
DORA mandates that financial institutions maintain strong “digital resilience,” which is the ability to withstand and recover from cyberattacks. One key requirement of DORA is Threat-Led Penetration Testing (TLPT); excerpts of the DORA requirements for TLPT follow:
Article 26.1 of the regulation explicitly states that Financial Entities shall “provide for advanced testing of ICT tools, systems and processes based on TLPT.” Article 26.1 provides extensive guidance on exactly what is required.
Article 3.17
Article 3.17 of the regulation explicitly states that “threat-led penetration testing (TLPT) means a framework that mimics the tactics, techniques and procedures of real-life threat actors perceived as posing a genuine cyber threat, that delivers a controlled, bespoke, intelligence-led (red team) test of the financial entity’s critical live production systems.”
Ready for DORA Compliance?
Get a personalized demo of the AttackIQ platform to test your security controls against DORA requirements. Identify gaps, optimize resources, and ensure your defenses meet compliance standards with executive-ready reports.